Kali Linux Social Engineering Pdf
A social engineering attack is a continuous process that starts with initial research, which is the starting phase, until its completion, when the social engineer ends the conversation. The conversation is a brief coverage of the four phases that the social engineer follows to perform an attack. Kali Linux Social Engineering - Rahul Singh Patel.pdf 3.8 MB Metadata.opf 2.11 KB Format: Retail PDF. Reader Required: Adobe Reader, Foxit, Nitro, Adobe Digital Editions.
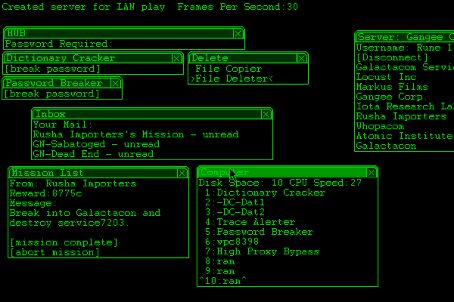
Effectively perform effi cient and organized social engineering tests and penetration testing using Kali Linux Overview • Learn about various attacks and tips and tricks to avoid them • Get a grip on efficient ways to perform penetration testing. • Use advanced techniques to bypass security controls and remain hidden while performing social engineering testing In Detail Kali Linux has a specific toolkit that incorporates numerous social-engineering attacks all into one simplified interface. The main purpose of SET (social engineering toolkit) is to automate and improve on many of the social engineering attacks currently out there. This book is based on current advanced social engineering attacks using SET that help you learn how security can be breached and thus avoid it. You will attain a very unique ability to perform a security audit based on social engineering attacks. Starting with ways of performing the social engineering attacks using Kali, this book covers a detailed description on various website attack vectors and client side attacks that can be performed through SET. This book contains some of the most advanced techniques that are currently being utilized by hackers to get inside secured networks.
Trusted value and performance. Browse products, accessory store, get support, register your products and find where to buy. Driver eMachines G720 Notebook for Windows 7. Attention:Please read the description first before downloading file in order to get the best compatibility of your notebook drivers specification and hardware built inside. To Download eMachines Notebook G720 Drivers you should Download Our Driver Software of Driver Navigator. Then you can download and update drivers automatic. Just Download and Do a free scan for your computer now. Acer emachines e725. To download Acer eMachines G720/G520 (Danube) Service Manual follow the instructions on the page. Download emachines g720 drivers windows xp broadcom. Download The Latest Acer eMachines EM250-1915 Windows XP Drivers This Acer eMachines EM250-1915 Windows XP driver disk is, in our opinion, one of the best ever released.
This book covers phishing (credential harvester attack), web jacking attack method, spear phishing attack vector, Metasploit browser exploit method, Mass mailer attack and more. By the end of this book you will be able to test the security of any organization based on social engineering attacks.
What you will learn from this book • Clone websites to gain a victim’s passwords and security information • Undertake credential harvester attacks through spear-phishing and web jacking • Perform client-side attacks through SET • Get hands on with practical advice on eliciting identity details • Counteract these techniques if they are being used against you Approach This book is a practical, hands-on guide to learning and performing SET attacks with multiple examples. Who this book is written for Kali Linux Social Engineering is for penetration testers who want to use BackTrack in order to test for social engineering vulnerabilities or for those who wish to master the art of social engineering attacks.
List of Free Kali Linux Hacking eBooks Download In PDF 2017 Ethical Hacking, Hacking ebooks pdf, Hacking ebooks free download, hacking ebooks collection, Best Hacking eBooks. List curated by Hackingvision.com Disclaimer The contributor(s) cannot be held responsible for any misuse of the data. This repository is just a collection of URLs to download eBooks for free. Download the eBooks at your own risks. DMCA takedown cannot be possible as we are not republishing the books/infringement of code, but we are just hosting the links to 3rd party websites where these books can be downloaded. To know more on DMCA takedown policy here. Kali Linux Hacking eBooks Download In PDF 2017 • • • • • • • • • • • • • • • • • • • • • • • • • • • • • • • • • • • • • • •.